The amount of new cybersecurity threats and vulnerabilities that organizations respond to grows every day. In many cases Zero Trust Networks (ZTN) are better equipped to tackle these challenges than traditional perimeter-based networks. Further, Zero Trust principles are becoming a critical part of the overall corporate strategy as organizations pursue larger digital transformation efforts. Understanding these Zero Trust principles and how to implement them is crucial to securing corporate data in this new era.
Why Use Zero Trust?
As technology evolves and security and privacy standards are developed and enforced (especially as workplace norms around employees working remotely evolve as a result of the COVID-19 pandemic), organizations need to take a stricter stance on strengthening the protection of data and systems. The following challenges are representative of where ZTN can be an effective solution:
- Security of Rapidly Changing Network Perimeter
ZTN enables businesses to maintain security of dynamic changes in the network architecture, especially when networks are spread across cloud environments and on-premise.
- User Accountability Concerns
ZTN utilizes granular user access controls to enforce access accountability and associated user actions by having an “authenticate first” approach.
- Too Many Security Tools
Most organizations do not have the resources to support the overabundance of security tools that are required to keep the enterprise network safe.
Five Best Practices for A Zero Trust Implementation
The foundation of a successful Zero Trust implementation is firmly dependent on five core concepts. These concepts not only assist in building a robust ZTN foundation, but they also allow the process to be sustainably and efficiently embedded into the way security is handled at an organization.
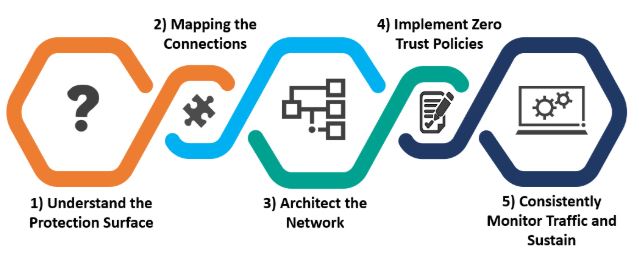
1) Understand the Protection Surface (Not the Attack Surface)
Regulatory privacy requirements and guidelines (e.g., General Data Protection Regulation, California Consumer Privacy Act, etc.) are on the rise, which make it essential for organizations to clearly identify their crown jewels and protect them accordingly. Privacy requirements and guidelines, and ZTN share a core component: the organization’s data.
Formally identifying and documenting the type of data that is critical to an organization and understanding where it is stored is essential in outlining the protection surface.
2) Map the Connections
A standard network architecture diagram that outlines traffic flow across the network is not enough. For ZTN to be effective a comprehensive map of the various connections throughout the network are also required.
Zero Trust requires a comprehensive mapping of the applications in use, associated data sets, and the connections where data is transmitted, with enough detail to determine where security controls are required.
3) Architect the Network Using Micro-Segmentation
The focus now shifts to utilizing tools and technologies to micro-segment the protection surface. Some of the current popular information security tools are firewalls, deep packet inspection tools, intrusion prevention systems and data loss prevention tools. These tools can be effective in building out the Zero Trust environment but need to be enhanced to assess and control traffic across the stack.
Security tools must be implemented and configured to identify, protect, detect, and respond to potential malicious activity, as well as implement micro-segmentation.
4) Implement Zero Trust Policies
Developing and implementing policies is one of the most critical and time-consuming steps to create a strong ZTN. It requires that organizations truly understand their protection surface, so that appropriate traffic flow is accepted or denied. These granular policies should be enforced on all network workload via security tools.
When developing and implementing Zero Trust policies, the key is to determine answers to the following questions: Who are the users? What do they need to access? When do they require the access? Where are the users and endpoints located that are requesting access? Why is access being requested to the data? And finally, how is the organization approving or allowing access?
5) Consistently Monitor Traffic and Sustain
Funneling all logs to a centralized location and monitoring them for malicious activity will allow all resources to be better protected. This can be done by using deep packet inspection tools and other network security monitoring technology. Further, automation and orchestration can be utilized to effectively monitor and block traffic that is unwanted.
Zero Trust is a continual process, thus inspecting all logs and making adjustments to gain additional visibility into all resources should be refined routinely.
Items to Consider When Implementing Zero Trust
Companies often view a move to Zero Trust Networking as a major effort that requires starting from scratch and rearchitecting their network and potentially buying several new tools. This is generally not true; many of the projects that a security organization has already delivered can be leveraged in the move to ZTN. For example:
- A successful Cisco ISE rollout can support many of the remote access and network access control efforts in support of ZTN
- A logging and monitoring project ensuring all logs are being captured and delivered to a centralized location can support the required monitoring efforts
- Deployment of a tool such as Netskope or Palo Alto Prisma can assist in providing coverage and visibility into SAAS applications.
These are all projects that are likely done as part of a mature security program and can be used to support the move to ZTN.
Finally, ensuring employees are trained and aware of the changes is critically important. Security personnel require training to better understand ZTN principles and its impact on the traditional security mindset. The broader workforce should also have a general understanding of how these changes support data security, contribute to alignment with security and privacy standards, and, mostly importantly, protect customer data and company/brand reputation.
The move to a Zero Trust model can be challenging. However, a thoughtful, measured approach that leverages appropriate technology, focuses on data security, and properly considers the business’s key goals and objectives, will contribute to the success of an organization’s Zero Trust journey.
To learn more regarding the basics of ZTN, please refer to our recent blog, “Is Software Defined Perimeter the Best Method for Adopting a Zero Trust Strategy?“
To learn more about Protiviti’s security and privacy capabilities, contact us.





