Each year, Oracle rolls out quarterly updates for its cloud applications as a strategic investment towards continuous innovation, new features, and bug fixes. All Oracle cloud clients are entitled to four feature updates each calendar year. On average, just in the cloud ERP space, more than a hundred new features (or functionality enhancements) are being made available each quarter. In some cases, it may even become overwhelming for organizations to understand, evaluate and distinguish new features which have been introduced as part of these quarterly updates.
The latest release (20D) for Risk Management Cloud was published on October 28, 2020. To enable organizations to take advantage of the updates, we have explained and simplified some of the key changes specific to Risk Management Advanced Access Controls.
Advanced Access Controls 20D: Enhancements
New Models and Existing Entitlements Revision:
Eight new models have been introduced – five models for segregation of duties and three models for sensitive access. Additionally, three entitlements that affect several existing out-of-the-box models have been revised.
The new models can be located within the Advanced Access Controls module under the respective product area (Enterprise Resource Planning Library, Human Capital Management Library, Supply Chain Management Library or Common Setup Library). A new model can be leveraged by selecting it and importing it into the application.
- New Models:
- 5241: Enter Accounts Receivables Invoice and Enter Journals
- 5242: Enter Accounts Receivables Invoice and Post Journal Entry
- 6924: Manage General Ledger Allocation Formulas and Generate Journal Entries from Allocation Formulas
- 5898: Manage Approved Supplier List and Create Purchase Agreements
- 5899: Manage Approved Supplier List and Create Purchase Orders
- 9804: Sensitive Purchasing Privileges
- 4574: Create Customer and Create Sales Order
- 9805: HR Sensitive Access Analysis for Excluded Roles
- Revised Entitlements
| Change | Entitlement | Privilege | Models Affected |
| Add Privilege | Create Purchase Orders | Generate Purchase Order | 5970: Create Purchase Orders and Create Payments
6080: Create Purchase Orders and Define Procurement Approval Routing Rules 6090: Create Purchase Orders and Approve Payables Invoices 6120: Create Purchase Orders and Create Payables Invoices 6190: Create Purchase Orders and Receive Goods and Services 6210: Create Purchase Orders and Return Goods and Services 8990: Create Purchase Orders and Manage Payables System Option 9370: Enter Budget and Create Purchase Orders 6820: Enter Journals and Create Purchase Orders 9013: Merge Suppliers and Create Purchase Orders 7620: Post Journal Entry and Create Purchase Orders |
| Remove Privilege | Create Purchase Orders | Change Purchase Order as Procurement Requester
Retroactively Price Purchase Order |
5970: Create Purchase Orders and Create Payments
6090: Create Purchase Orders and Approve Payables Invoices 6120: Create Purchase Orders and Create Payables Invoices 6190: Create Purchase Orders and Receive Goods and Services 6210: Create Purchase Orders and Return Goods and Services 6410: Create Suppliers and Create Purchase Orders 6820: Enter Journals and Create Purchase Orders 7620: Post Journal Entry and Create Purchase Orders 8181: Item Costing and Create Purchase Orders 8220: Receipt Accounting Activities and Create Purchase Orders 8990: Create Purchase Orders and Manage Payables System Option 9013: Merge Suppliers and Create Purchase Orders 9370: Enter Budget and Create Purchase Orders 5899: Manage Approved Supplier List and Create Purchase Orders |
| Add Privilege | Create Suppliers | Manage Supplier Profile by REST Service | 5897: Create Suppliers and Receive Goods and Services
5980: Create Suppliers and Create Payments 5984: Create Suppliers and Create Purchase Agreements 5985: Create Suppliers and Maintain Supplier Bank Accounts 6370: Create Suppliers and Approve Payables Invoices 6390: Create Suppliers and Create Payables Invoices 6410: Create Suppliers and Create Purchase Orders |
| Add Privilege | Sensitive Human Resource Privileges | Pending Worker Quick Hire
Manage Mass Updates Work Area Perform Worker Mass Legal Employer Change Perform Worker Local and Global Transfers |
4079: Sensitive Human Resource Privileges |
Table source: Oracle Cloud Readiness | Oracle Cloud
Ability to Combine up to Three Entitlement Filters
Prior to 20D, Access Models could be created with up to two entitlements, allowing organizations to evaluate users with access to two conflicting entitlements (e.g., Enter Purchase Order and Enter Invoice). If an organization had three-way SoD risks within their ruleset or risk framework (e.g., Enter Purchase Order and Enter Invoice and Enter Payment), they were forced to adjust their ruleset or create two two-way risks and compare the outputs.
Fortunately, with release 20D, the application now allows the creation of Access Models with multiple filters if there are no more than three entitlement-based filters amongst them. With the ability to add up to three entitlement-based filters, organizations can be more specific about the control in the specific model definition, resulting in fewer false positives.
The screenshot below shows a three-way model configured within the application (Enter Journals and Post Journal Entry and Manage Accounting Period Statuses for General Ledger).
Source of screen shots: Oracle Cloud Readiness | Oracle Cloud
Enhancement to Result Analysis Capabilities
Post ERP go-live, it is not typically common for application security to be completely clean and conflict-free. Hence, when Advanced Access Controls is enabled, initial output may show thousands of incidents pending for necessary resolution/action.
One common request from Risk Management Cloud clients was to have functionality allowing users to understand and address access incidents in an organized manner. This gap has been addressed in 20D release, with the introduction of two new pages in the Advanced Controls Results Management area:
- Access violation summarized by Control and the User, and
- Access violations summarized by Control, User, and Role.
The primary purpose and benefit of these new pages is to make it easier for all the result investigators to decide or take required action based on summarized / clustered results instead of individual lines of data.
The below screenshot shows the newly introduced columns on the Control Summary page – User Count and Result Count. Clicking on these headers navigates to the two new pages.
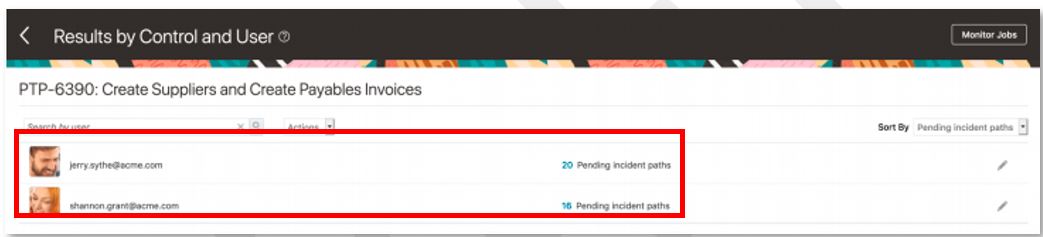
As highlighted below, the new page Results by Control and User displays the summarized incident results for the relevant control, broken down by each user who owns the incidents.
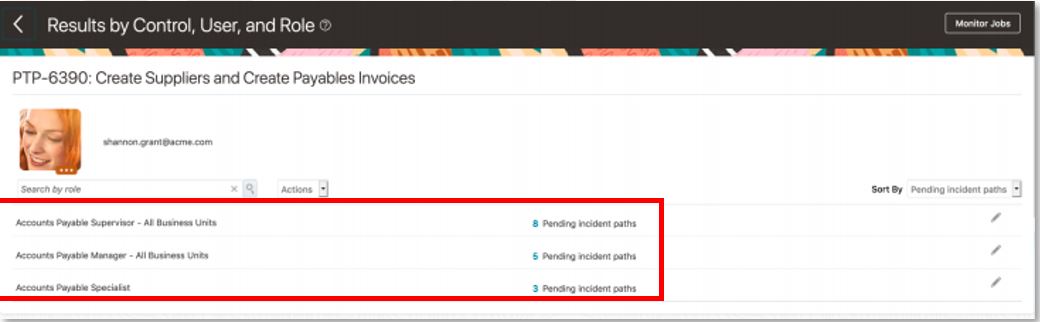
As highlighted below, the new page Results by Control, User and Role displays the summarized incident results for the relevant control, broken down by the user who owns the incident and the roles assigned to that user.
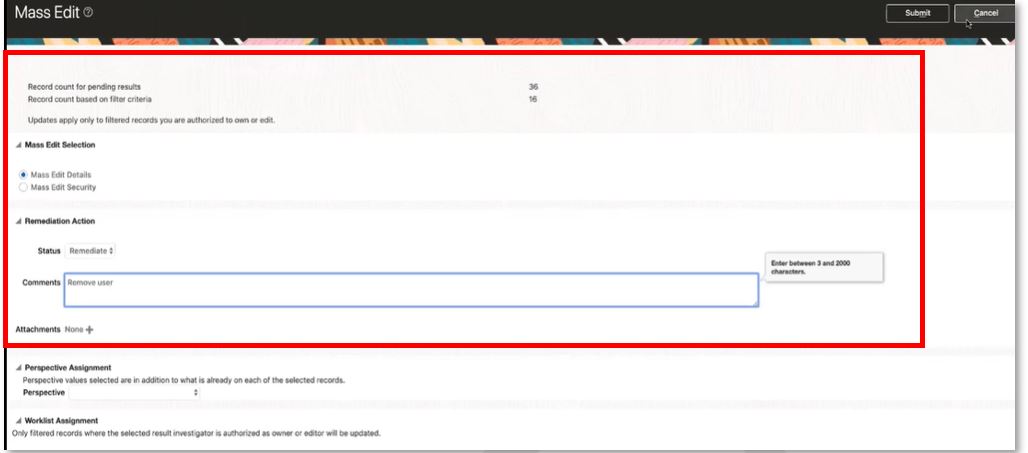
The user can also act against each row by mass editing the incidents. For example, in the below case, the user can mass edit all the pending incidents for the selected user and role combination, with a remediation action to remove the Accounts Payable Manager role from the user.
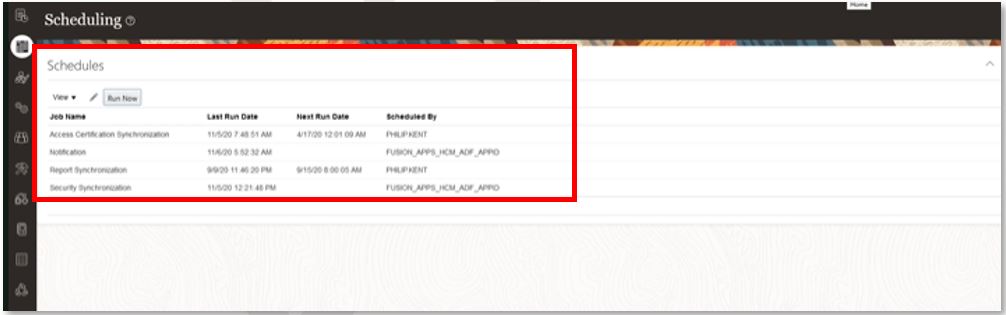
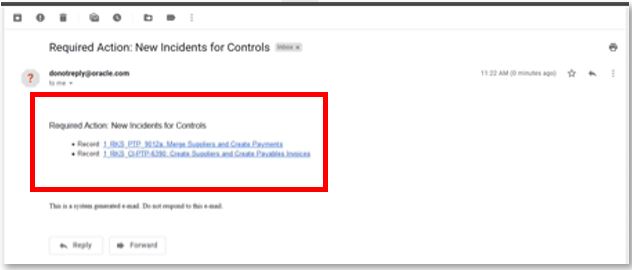
Email Announcement of New Control Results is Consolidated
This feature sends a consolidated email to all authorized recipients containing a list of all the Advanced Controls which have generated at least one new incident which the recipient is authorized to edit or own. An incident is treated as new if it was generated after the last time the recipient was alerted.
This feature will reduce the volume of emails that a single user will receive from the Risk Management application, leading to increased efficiency and early action.
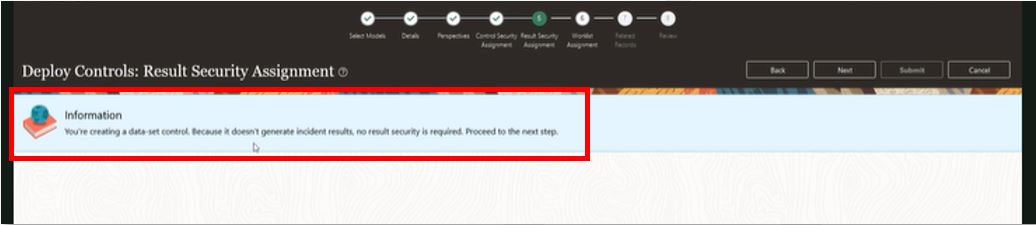
Data Set Advanced Controls No Longer Requires Result Security Mapping
This enhancement removes the requirement to define result security while defining an Advanced Access Control with result type as data set. (Note: An incident control generates records of access assignments or transactions that may violate risk definitions, while a data set control generates data to be included in a user-defined object.)
Going forward, while deploying an access model as a control, after the user provides the value for control priority and changes the result type to Data Set, the system will display a message that “no result security is required.”
Conclusion
To summarize, we explained and highlighted the various enhancements introduced in release 20D for the Advanced Access Controls related to:
- Addition of new models and modifications of entitlements within existing models,
- Enhancements related to the creation of three-way models
- Summarized access model results reporting capabilities,
- Consolidating email notifications of control results, and
- Removal of security setup for the Data Set Advanced Controls
Oracle continues to enhance their Risk Management product to improve functionality and end user experience. Don’t miss our next update after release 21A — become a subscriber to our Tech Insights blog by clicking Oracle (as well as other topics of interest) and completing the form to the right of this post.
To learn more about how Protiviti can help with Oracle, please visit our Oracle Solutions site or contact us.
To stay informed about future Oracle updates via blogs like this one, subscribe to our Tech Insights blog. Simply fill out the subscription form at the top right of this page and check the Oracle box to receive notifications when new blogs are posted.