Workday’s object-oriented architecture and robust reporting engine enables financial and human capital data management and analysis within a single platform, unlocking possibilities for powerful new insights. To a new user, the complexity can feel daunting—so where to start? Let’s take a closer look at how to quickly get up to speed, access some of the most valuable standard (out-of-the-box) reports and share tips on how to leverage and customize standard reports to get the data needed.
The best place to begin exploring Workday reporting is to become familiar with the Workday-delivered, out-of-the-box reports. Enter Workday standard reports into the search bar for a full list of delivered reports. 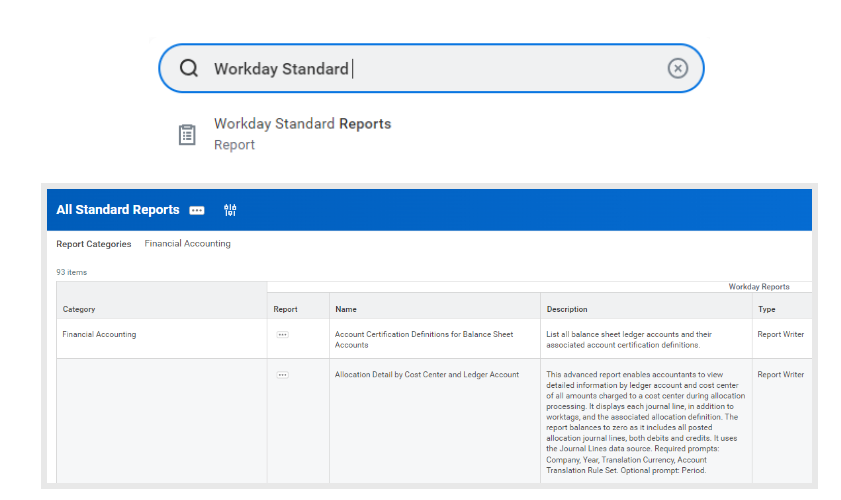
Browsing this comprehensive listing of reports can help users get familiar with available reports and potentially discover that a suitable report may already exist. Here, it is possible to find basic information such as category, description, type of report, whether the report is schedulable and the domain. It is easy to add a category filter such as financial accounting (as shown above) to narrow the list.
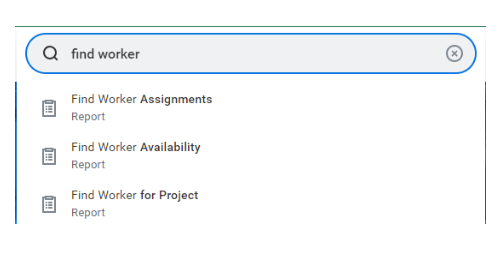
Finding individual reports is just as simple. Start by typing find, view or extract in the search bar to explore the options. For example, to locate specific employee information, type find worker or view worker” and click directly into one of the top choices via the drop-down options.
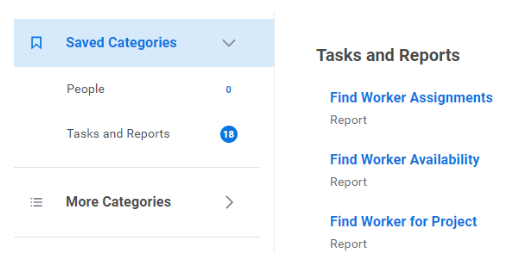
Alternatively, to see a full list of reports, tasks, and other related items, hit enter after search and navigate to the tasks and reports tab to view a full listing.
Reports, like other objects in Workday, are controlled by security group assignments. Standard reports can generally be accessed by the auditor and report writer security groups; custom reports need security group access assigned at a per-report level. In the case where a report cannot be found, contact the Workday Security Administrator to assist with determining the need and with granting access.
We have included below a handful of commonly used reports that provide quick value for the average user. Some of these reports, like find supplier invoices, will provide key data for executing daily tasks. Others can help overcome obstacles; for example, when searching for a task or report yields no result, security access is likely the issue. The report view security for securable items will reveal the security permissions required to access that object.
| Business function | In order to | Search |
| Cross-functional | View the organization structure in a hierarchy format | Org chart |
| View all BPs (Workday business processes or configurable workflows) | Business process booklet | |
| View a log of changes made to Workday objects (useful for auditors) | Audit trail – business process
Audit trail – custom report Audit trail – integration Audit trail report Audit trail |
|
| Human capital management (HCM) | View employee data for selected supervisory organizations and subordinates | Employee by organization |
| Review hires and terminations activity on a quarterly basis over multiple quarters / years | Hires and terminations by quarter | |
| View headcount by supervisory organization by month and visualize the headcount trend | Headcount and FTE by month | |
| Finance
|
View accounts payable (AP invoices) by vendor, date and status | Find supplier invoices |
| View a list of journal entries | Find journals | |
| View data about multiple transactions (purchase orders, purchase requisitions, expense reports, invoices and journals) | Find journal lines | |
| Compare bank statement balances and ledger bank balances in a summarized format | Book to bank summary report (and sub-reports) | |
| View open purchase orders with remaining balances by cost centers | POs with open encumbrances by organization | |
| Security | View the security permissions required to view or modify a particular object or to act within a BP | View security for securable item |
| View workers assigned specific security roles and details around the roles | View security groups
View security groups for user |
Workday offers an array of options for creating custom reports. Users with access to the report writer security group can parse the wide range of Workday data sources to put together a report with only the information required. Custom reports can be shared, edited and scheduled as needed. A note of caution: the need for identification and development of Workday custom reports should be coordinated and governed appropriately to prevent report proliferation and redundancy within the Workday tenant.
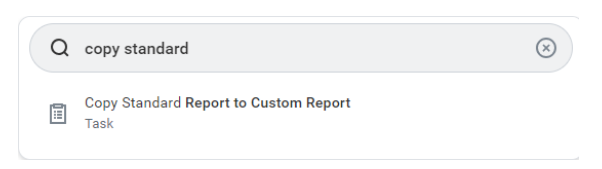
Creating custom reports can be time- and labor intensive. Before creating a report from scratch, check whether there is an existing standard report with an output that is similar to the desired output. If so, save time by copying that standard report into a custom report: instead of building a report from scratch, simply tweak an existing report by adding or modifying a column or field.
How to copy and modify a standard report:
- Search copy standard report to custom report in the task bar
- Fill in the prompt for the standard report name
- Rename the report accordingly, select OK and make necessary adjustments
It is also possible to use this task to remove information from a custom report to produce a more concise output or to make updates if business needs have changed. Overall, this is a fantastic resource for report writers, both new and experienced, to meet specific reporting requirements.
Whether using Workday reporting to regularly obtain operational insights or answer ad-hoc requests, audit worker information or feed data to an integration, Workday reporting is a powerful tool to address wide ranging business needs. Learning and understanding Workday’s reporting functionality makes it possible to amplify its power to deliver insights and remain agile in an ever-changing business environment.
Jerine Hu, Senior Manager – Business Platform Transformation, also contributed to this blog.
To learn more about our Workday solutions, contact us.