Traditionally, it has been a conundrum for many CISOs and CIOs working with SAP products on what is truly needed to ensure the security of their data for sensitivity or competitive advantage purposes. Standard Security Information and Event Management (SIEM) monitoring often fails to ensure the security of the SAP system because the specific SAP logs and analyses can’t be interpreted, and, consequently, attack patterns cannot be identified or recognized. In this post, we discuss why this is the case, what companies can do to integrate SAP in their monitoring nonetheless, and how this end-to-end safeguarding can deliver additional benefits.
SIEM safeguards the security of IT environments by combining security information management (SIM) with security event management (SEM) to generate real-time analyses of security alerts. The collection, correlation and analysis of log data, system messages and signs can identify attacks, unusual usage patterns and dangerous trends. As such, SIEM provides an overview of security-relevant events in IT environments, helping to meet legal requirements and satisfy internal policies and compliance rules for IT security. The critical tasks: provide reports on security-relevant incidents, such as successful and failed login attempts, as well as malware and other potentially harmful activities, and send notifications when an analysis indicates that an action violates the defined rule sets and is therefore indicative of a potential security problem.
How SIEM works
When data is consolidated in one place, critical activities can be identified earlier through analysis patterns and trends. The data is collected and interpreted in real-time, and the information gained is saved in an unalterable form. Commonplace sources for SIEM include servers, firewalls, routers, intrusion prevention systems (IPS) and intrusion detection systems (IDS). Their data is forwarded to a central point, saved, normalized, structured and analyzed for storage. The analyses use defined rules, correlation models, machine learning and artificial intelligence to generate relations between the entries and identify anomalies.
In contrast to other security measures, attacks are not prevented in advance, but their impact and spread can be reduced through alerts. Such alerts and automated reports enable responses to a variety of threats in real-time, as well as subsequent documentation of security incidents. However, SAP systems are more nuanced.
Parallel worlds: SAP and SIEM
There are several reasons why SIEM and SAP have been disconnected from each other from the outset: SIEM originates from classic network technology, from a historic era of using operating systems under DOS and networking technology based on Ethernet with large, standalone mainframe applications for financial and managerial accounting, controlling processes and more, all independent of one another. As IT became more interconnected, SIEM was introduced to monitor events in the network layer – questioning where the information originated from, who accesses it, what is already known, and what doesn’t fit established patterns. In this approach, rule sets and IT controls are crucial: they are used to check occurrences in the network and draw conclusions for security analysts. As such, traditional SIEM tools consider IT infrastructures, not individual applications.
In recent years, it has become increasingly apparent that applications also must be included, whether Microsoft Dynamics, a product planning tool or an SPS in production. This is followed by a big ‘but’ where SAP is involved: SAP is much different from other applications and is essentially a network of its own. Users can do many different things with SAP, both with roles and authorizations and about security. While many of the mechanisms are similar to others in IT, SAP differs in its nomenclature and rule sets. When it comes to network equipment and the rest of IT, SAP is unique in language and diction. That’s why many companies still draw a line between SAP and their other IT security monitoring systems.
SAP is ignored by SIEM – but it doesn’t have to be
Conventional SIEM tools concentrate on identifying unusual behavior within infrastructures, but SAP systems are often ignored. If no access is provided to the SAP system, SIEM can identify little more than a kind of ambient noise of logs with millions of entries which are difficult to interpret. In other words: SAP systems represent a blind spot for most SIEM tools because they don’t include SAP-specific checking rules. This means they don’t recognize corresponding attack patterns, so security teams fail to identify specific threats and incursions.
Furthermore, exceptions in the SAP system may appear trivial at the network level. The only way to identify them is to consider the context of the application itself. As a result of these comprehension problems, many teams ignore SAP altogether or tackle it last because it’s easier to deal with recognizable occurrences. That’s why SAP is often neglected: even companies that manage highly professional IT security teams, using SIEM technologies and mastered all non-SAP areas tend to overlook SAP. CISOs at companies that use SIEM should ask themselves: am I sure I am giving my SAP systems enough attention? If not, it simply makes sense to combine the two worlds.
The best of both worlds
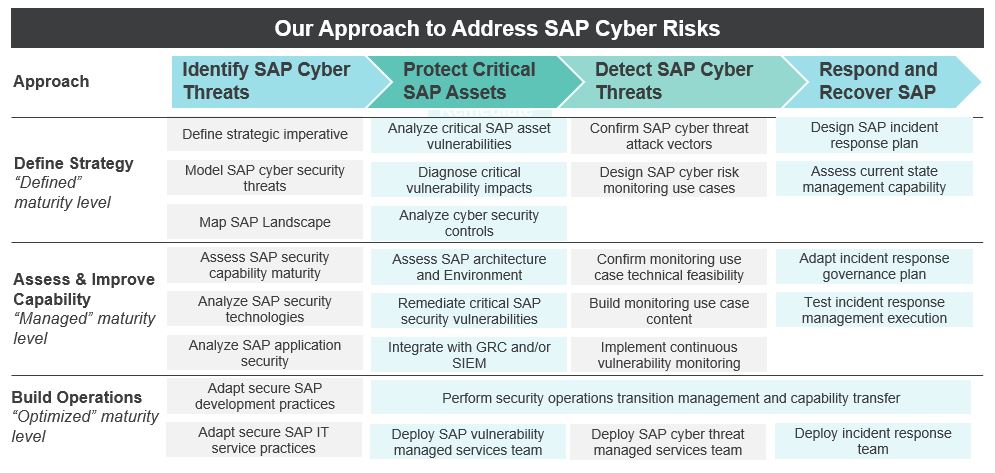
Network specialists have created efficient tools to provide an overview but often forget there are other worlds besides theirs, therefore achieving proper end-to-end protection requires bringing both worlds together for the company’s benefit. Detecting attacks based on log files and analyzing network traffic requires in-depth knowledge of the potential paths and patterns such incursions can follow. Intelligent information management is necessary to assess security data of this kind. Events relevant to security must be filtered out of a sea of data and placed in the proper context so that companies can use their security function as a competitive advantage with the rapid pace of their business transformations. This is where software like Onapsis and ETD (Enterprise Threat Detection) comes in, extracting events from the application layer and transporting and translating them so that SIEM environments can consume and understand more easily. SAP systems continue to undergo tremendous transformation from being back-end systems to being the centerpiece of the business and customer experience engine. To keep up with this shift in thinking, we would recommend taking a holistic look at SAP environments, treating them with the same rigor as the rest of the enterprise, while continuing to explore the technology innovation and automation opportunities available.
To learn more about our SAP consulting services, contact us.