In order to enhance their approaches to cyber and other risks, many organizations are integrating security, privacy, policy and controls into their DevOps lifecycle, processes and tools. As the DevSecOps trend gains momentum, we anticipate more organizations will make threat modeling, risk assessment and security automation integral components of their product development initiatives, from ideation to iteration to launch and ongoing operations. DevSecOps fundamentally transforms cyber and risk management from compliance-centric activities (usually considered later in the development lifecycle) into fundamental framing mindsets across the product development lifecycle. DevSecOps embeds policies and best practices into tools and underlying platforms, enabling security to become a collective responsibility of the entire IT team. For organizations that have not yet begun the DevSecOps journey, here are three important things to know now.
- What is DevSecOps?
It is a transformation that incorporates secure culture, practices and tools into each phase of the DevOps process. Leveraging DevOps’ ability to improve collaboration between development and operations teams while delivery speed utilizing automation technology, DevSecOps seeks to automate core security tasks by embedding security controls and processes into the DevOps workflow and automating code security and testing. 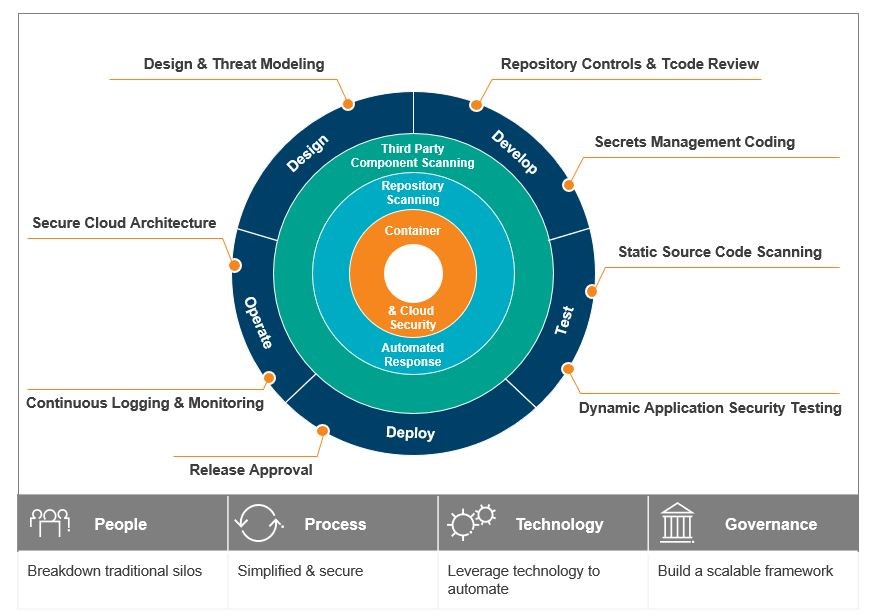 DevSecOps uses secure culture, practices and tools to drive transparency, teaming and agility in every phase of the DevOps lifecycle. Even though companies can tailor their security approaches to support their cyber program and product requirements, DevSecOps initiatives rest on four key aspects:
DevSecOps uses secure culture, practices and tools to drive transparency, teaming and agility in every phase of the DevOps lifecycle. Even though companies can tailor their security approaches to support their cyber program and product requirements, DevSecOps initiatives rest on four key aspects:
People. When you integrate security into your DevOps pipeline, people are still your greatest asset. In a regular waterfall model, development, security, and operations teams work in silos. As the organization transitions to DevSecOps, teams may still operate that way for a while — breaking down those traditional barriers can be the most crucial enabler to the DevSecOps process. By identifying and getting rid of those silos fast and creating shared goals across the teams, DevSecOps can drive a culture of innovation that compromises openness, transparency and ownership across development, security and operations teams.
Process. Speed and quality are essential to DevSecOps. Simplifying the manual processes without sacrificing cybersecurity needs is a crucial measure. Now that development and deployment are accelerating much faster than before, security software development processes should become more automated and channelized. If not, efforts to exponentially accelerate secure software deployments may not sustain.
Technology. DevOps has created an abundance of cloud-based solutions that developers are using to accelerate delivery. Thankfully, cybersecurity software is now beginning to keep pace. Take an incremental approach to technology deployment by testing these new security tools with specific product teams before releasing to the enterprise.
Governance. The term governance is very broad, but there are two ways to think about governance for cybersecurity in the world of DevSecOps:
- Micro-level: Embedding cybersecurity into DevOps can boost efficiency in governance. DevSecOps, by design, requires a very consistent process that uses a uniform set of tools and automated controls. This simplifies the monitoring and testing of required controls.
- Macro-level: DevOps has transformed how IT organizations work. In some companies, IT operations—traditionally comprising a mix of senior management, management, and engineers—is moving to a flatter hierarchy made up of fewer management positions supported by architects and engineers.
Like any other IT program, DevSecOps should directly tie to your broader IT strategy—which, in turn, should be driven by the business strategy. If a DevOps program supports both IT and business strategies, then embed the “Sec” at the same time. In short order, it may help the organization bolster its cyber maturity posture and eliminate the need to rework the DevOps program later, when it’s much harder to do.
- Is the Organization Ready for the Journey?
Embedding security into DevOps pipelines may seem like an obvious proposition. If DevSecOps is just a thought process to incorporate security, then deploying it into the DevOps lifecycle should be simple. For those few who have mastered DevOps, perhaps. For others — that is, for most — developing DevSecOps practices will be another component in existing DevOps initiatives that are still in initial stages. As an example, in their 2018 Global Developer Report, GitLab surveyed approximately 5,300 IT professionals about their DevOps lifecycle experiences. Thirty-five percent of respondents said DevOps culture at their companies was “somewhat established.” Only 23 percent of those would go so far as to describe their development method as DevOps.
DevSecOps is not a security trend in and of itself but, rather, an aspect of the ongoing DevOps revolution. It is more of a mindset than a defined set of rules. Organizations should consider these important characteristics of DevSecOps, which differ from a traditional security approach, to evaluate if the culture is ready for a shift to DevSecOps thinking:
- Open collaboration on shared objectives. DevSecOps creates common expectations and metrics for measuring success. It aligns security architects and focuses on business priorities.
- Security at the source. DevSecOps have adaptable, self-service security potentialities enable security guardrails and make it possible for teams to monitor results and provide constructive feedback. It can identify cyber vulnerabilities early in the application development lifecycle, decreasing the probability of rework during or post-deployment.
- Reinforce and elevate through automation. By automating repeatable tasks, DevSecOps enables an integrated process flow, embeds preventative operational controls, and creates ongoing audit trails.
- Risk-oriented operations and actionable insights. Organizations incorporating DevSecOps into their development lifecycle can use operational insights and threat intelligence to drive process flow, prioritization, and remediation recommendations. They no longer must rely only upon code scans and can take a more risk-based approach to testing.
- A holistic approach to security objectives. Integrated frameworks allow securing both the pipeline and application. This helps create a more comprehensive, end-to-end defensive mechanism throughout the production environment.
- Proactive monitoring and recursive feedback. Automated, continuous testing helps to identify issues before they become problems. Developers can also leverage the logs to drive innovation.
- Automated operations security. Visibility into some aspects of operational security can be a challenge. CIOs owning security audits often find themselves in an unfavorable position, assuming that security administrators have performed their jobs effectively. The latest techniques in containerization and public cloud infrastructure automation have increased the efficiency of security and compliance audits.
- Operations engineering. Human intervention in the intrusion detection process can burn through hours, or even days, of engineering time. However, insecure infrastructure-as-code environments in containers or public cloud/containerized environments engineered with capabilities can instantly redirect traffic, freeze nodes for later inspection, notify operators, and spin up new instances—all automatically.
Implemented together, these DevSecOps elements can help improve the overall quality of security, boost productivity, and reduce compliance issues.
- Change is Coming: Next Steps
The burning need to get quality products delivered faster has enhanced DevOps practices in the world of software development. In an organic extension of DevOps evolution, the DevSecOps trend offers CIOs and their development teams a new amalgamation of tools, practices, and automation that, deployed in concert, can help secure development and operations.
DevOps’ core value is “speed to market.” Organizations that do not consider and incorporate security in every phase of their development and operations pipelines take higher risks and become highly vulnerable. Every product you deliver should be of high quality— secure, tested, and reliable. No stakeholders should waste time on cyber surprises.
It’s high time to stop playing the patch management game with security.



