According to the recent survey conducted by North Carolina State University’s ERM Initiative and Protiviti (2019 Executive Perspectives on Top Risks), C-suite executives and board members continue to view cyberthreats as a top risk behind the risks of competing against “born digital” firms, retaining top talent, and regulatory changes. Additionally, these leaders continue to view identity management and information security as a top ten risk. The results of the survey further validate the need for strong security and compliance postures as organizations embark on digital transformation initiatives in order to stay competitive.
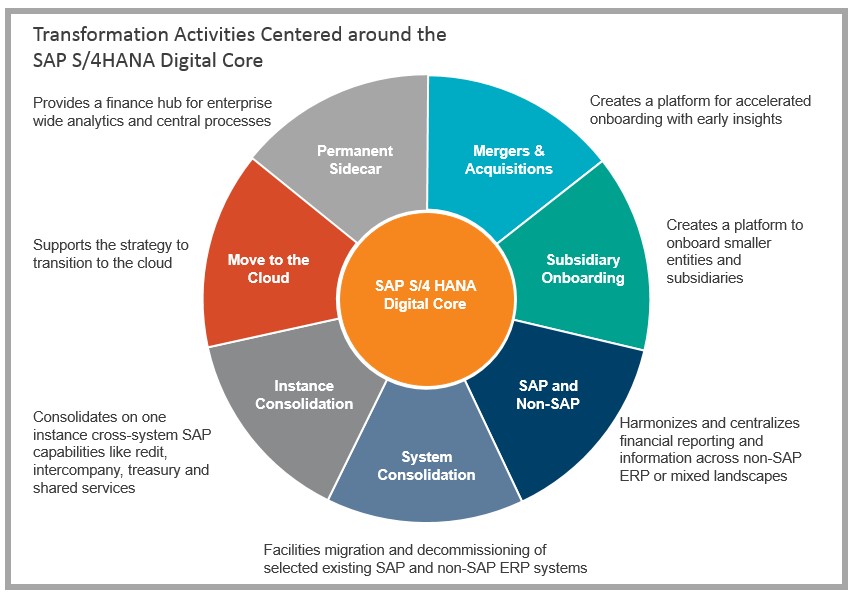
Historically, organizations have relied on SAP Access Control to monitor access risks against core business functions which have been centralized within a single ERP application. This idea of centralizing all core functions has flipped to a strategy of deploying best of breed applications specific to business functions in order to drive optimized process efficiencies. Organizations are also seeking to simplify management of their application landscape by moving them towards the cloud. Other organizations are taking a larger step by digitally transforming their organization and starting with the appropriate foundational elements such as S/4HANA or Central Finance to greatly drive efficiencies within their core back office functions.
As companies embark on transformation initiatives, it is critical they focus on access management efficiency while prioritizing key areas such as security, privacy, and compliance. Upgrading or implementing SAP Access Control 12 presents the perfect opportunity to modernize and transform identity and access governance. A critical date that should be considered when planning for changes is December 31, 2020. This is the date that mainstream support will be ending for Access Control 10.1. This is important to note as organizations should begin planning for their upgrades to ensure adequate time to complete the effort. While an upgrade from version 10.1 of Access Control may seem like more of a technical process, it creates opportunities to revisit additional functionality including the monitoring of cross-system access-based risks, improving the user experience, and implementing automation for low value, low-risk tasks.
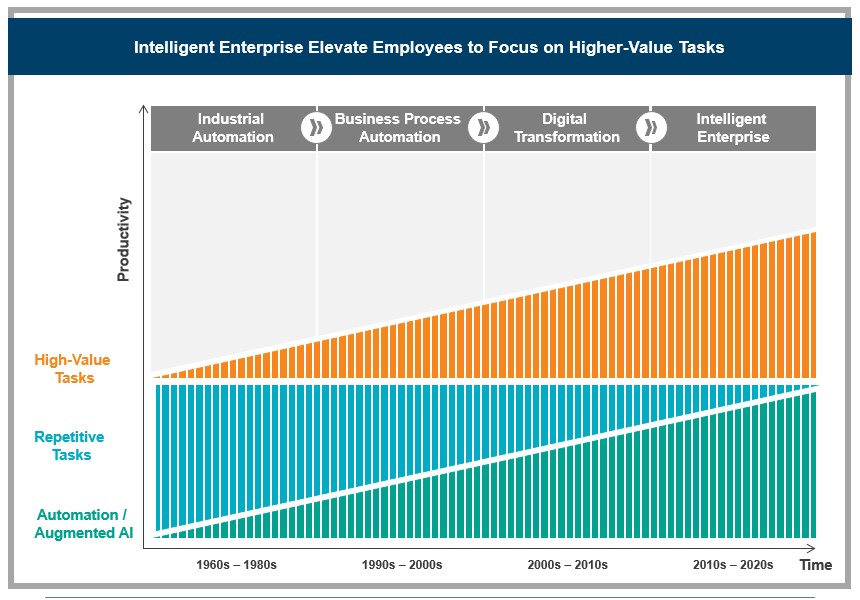
These shifts in technology and corresponding changes in processes allow organizations to revisit these potential massive changes in the risk landscape and to mature the tools which support governance around key applications. Details of these additional opportunities are outlined below:
Extend and Efficiently Manage Applications in the Cloud
- When integrated with SAP’s Cloud Platform, Access Control 12 can be used to manage user provisioning and risk analysis to a wider range of SAP products using out-of-the-box connections, including:
- SAP SuccessFactors Employee Central
- SAP Commerce Cloud
- SAP Ariba
- SAP S/4HANA
- SAP Concur
- Organizations should consider optimizing access risk rulesets to reduce security risk and improve visibility of access-based risks by reviewing and expanding segregation of duties (SOD) and sensitive access (SA) rulesets across other systems, including Fiori, S/4HANA, and HANA databases.
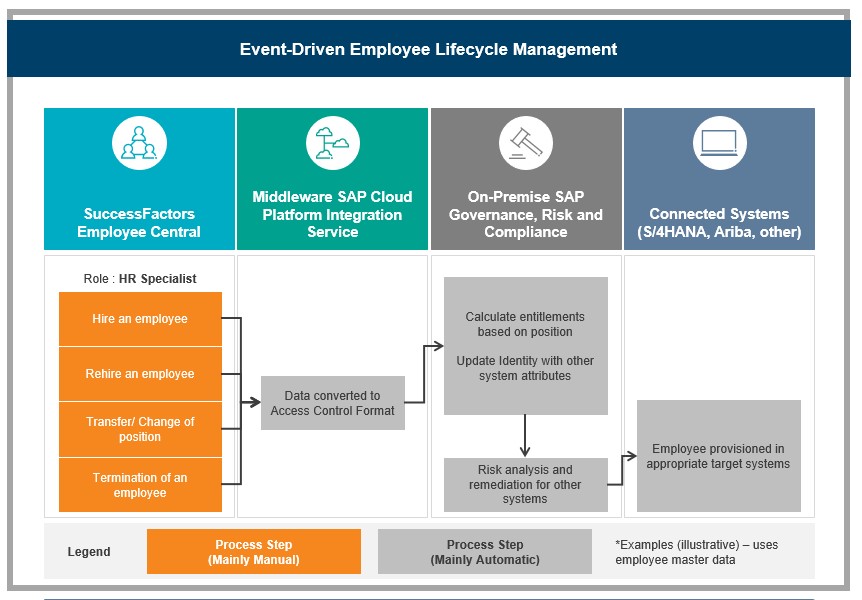
Significantly Improve and Automate Onboarding and Offboarding
- The latest version of Access Control is now fully integrated with SuccessFactors Employee Central. Organizations can integrate upstream in the onboarding and offboarding processes to trigger events in GRC based on actions taken in SuccessFactors. This is a significant step forward in being able to proactively manage changes to employee status for onboarding new hires, transferring employees, and terminating employees and adjust the end user’s access in downstream applications.
- Additionally, Access Control can be used to manage access within SuccessFactors and integrates with out-of-the-box functionality to provision access and perform risks analysis.
- The ability to integrate with the HR system is a core element of any identity management process and is an enhancement that closes the gap in the end-to-end access management process while providing automation and addressing key control areas.
An Opportunity to Improve the User Experience with Fiori
- In the most recent release by SAP, additional focus has been put on the user experience. Users are now presented with an interface aligned with the Fiori user interface.
- Traditional technical security roles have shifted towards five user-friendly Business Roles: Access Control Administrator, Access Control Employee, Compliance Manager, Request Manager, and Security Manager. These pre-defined business roles are provided as part of the upgrade, however, organizations have the ability to create their own. Each business role intends to simplify navigation and provide the user with just the functions for their role.
- Another new feature is the introduction of Overview Pages. These Overview Pages have been designed to serve as a dashboard for each core area of Access Control (access risk analysis, access request, emergency access, and role management). The visualizations often link back to existing reports but are much more visual and metric-based with the capability to be filtered by date range and system.
New and Notable Functionality Additions
- Firefighter functionality has been extended and made available for the HANA database layer and will utilize the same firefighter launchpad. Additionally, the audit trail will be customizable through the use of HANA audit policies.
- Improved dashboards (Overview Pages) provide real-time visibility and metric-based reporting
- Firefighter maintenance has been streamlined to eliminate duplicate maintenance of controllers and owners
- Additional user access review filters have been added to allow the review process to be refined and performed for specific business processes, role criticality, and functional areas.
- Synchronization jobs have been updated with performance improvements to reduce job run times and allow the jobs to run in parallel in order to optimize the data synchronization process
Visit Protiviti’s SAP consulting services page for more information on our solutions.






